In a recent partner hackfest, the need to store a Username/Password combination in Azure Key Vault arose. Setting up Key Vault instance was dead easy:
- Sign in to the Azure portal
- (optional) Find the Resource group that you’d like to add the Key Vault instance to
- Add a new Key Vault
- Start entering secrets
For the purpose of this hack, what I needed to store was a master username/password combination for accessing a Microsft PowerBI Workspace. The purpose of the hack was to demonstrate how to embed PowerBI Reports into your own website.
Problem
While developing the website locally, I could not, for the life of me, understand why I could not connect to Azure Key Vault from my developer computer. Any access to the vault would time out, and an error message from the call stack would indicate that 4 different methods we tested, and that none of them worked.
Solution
The solution was untraditional, hence why I am posting this as a reminder to myself:
When you’re developing a Web Application that utilizes Azure Key Vault, you need to make sure that you have the Azure Command Line tool installed. This tool will allow you to sign in to your Azure portal and create an access token that Visual Studio can see and use for the purpose of accessing Azure Key Vault.
What you do is:
- Download and install the azure command line tool (it exists for Windows, Mac and Linux)
- Run the installer according to the platform instructions
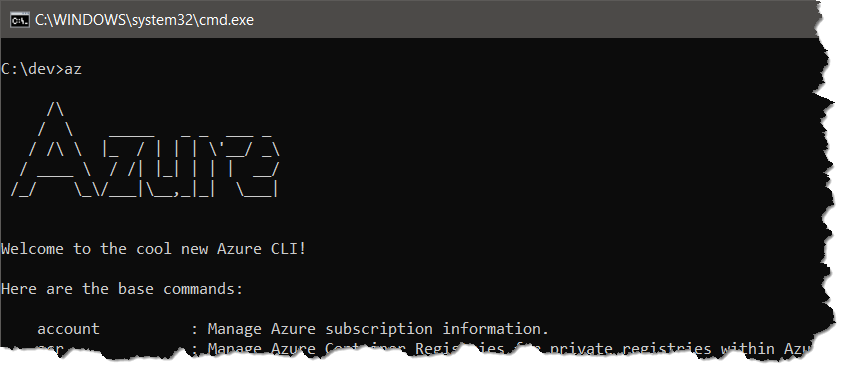
- Once completed, you should be able to type az in a new command window (powershell/cmd/shell/terminal etc)
The next step is to generate a cached token, you do this by signing in using your new CLI tool:
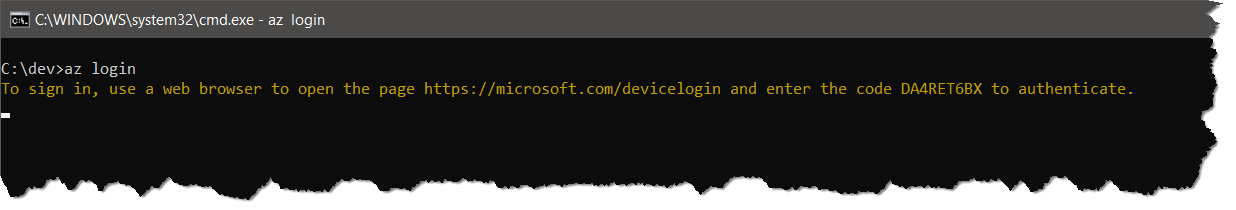
Once you complete the instructions on screen, you will see a JSON structure containing the details of your subscription. What you do not see, is that a token cache has now been generated that will allow you to debug your website, and utilize Azure Key Vault without any issues.
Enjoy 🙂




Most likely you would be using a key vault client that uses AzureServiceTokenProvider to authenticate with Key Vault. The AzureServiceTokenProvider uses different options to get a token to connect and using the token from the AzureCli is one of them. One another option on your local environment would be to set an environment variable with AzureServicesAuthConnectionString. the environment variable could use ClientId/Secret or ClientId/Secret authentication mechanism to authenticate with Key Vault.
However, I have not tested this in your particular scenario of using it from a Power BI Workspace.
Here are some reference links
1. https://docs.microsoft.com/en-us/azure/key-vault/service-to-service-authentication#connection-string-support
2. https://rahulpnath.com/blog/authenticating-a-client-application-with-azure-key-vault/